Encryption has become a key component of information protection within Microsoft 365 (and other platforms). While this is great from a security and data loss prevention perspective, there are additional complexities to consider with encrypted content in eDiscovery.
How does encryption work in Microsoft 365?
Documents, emails and meeting invites can all be encrypted in Microsoft 365. This is done by applying sensitivity labels with associated encryption settings.
Common use cases include:
-
- Ensuring confidential documents can only be opened by specific departments/users.
-
- Preventing specific information from being copied or shared outside of approved circles.
-
- Limiting editing rights to specified departments/users only, with others limited to read-only access.
-
- Preventing documents with time-limited relevance (e.g. price lists) from being opened after a specified expiration date.
-
- Restricting meeting invite access and sharing to approved participants only.
When applied, encryption settings ensure that content can only be decrypted by authorised users and remains encrypted (even if the file is renamed) regardless of whether it’s inside or outside the organisation, at rest, or in transit.
Why is encryption a challenge for eDiscovery?
Encryption reduces the risk of data loss and enhances information protection, but it can create blind spots during eDiscovery if it’s not processed correctly at point of collection.
In this, there are crucial differences in the capabilities of Microsoft Purview eDiscovery (Standard) and eDiscovery (Premium) with regards encrypted content in eDiscovery:
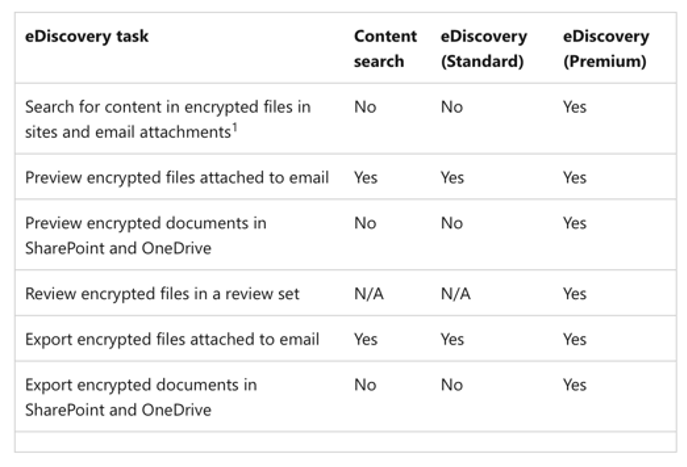
These differences can affect whether encrypted data can be searched, viewed as part of the eDiscovery process, and exported. Without fully understanding them, it’s very easy for blind spots to go unnoticed during the search/collection/export of data for further investigation.
These blind spots can be identified by reviewing the error files for data exports. At this point, however, decryption options are severely limited.
Pro tip: All encrypted data must be decrypted as part of the collection process – before issues are spotted at export. eDiscovery (Standard) has limited functionality where encryption is concerned (amongst other things). That makes it important to know at the beginning of an eDiscovery case whether sensitivity labels are in place, and whether the eDiscovery tools in use have the capability to handle the decryption.
A cautionary tale about encrypted content in eDiscovery
A Salient client required data collection for an eDiscovery case. Their CIO commissioned their third-party IT provider to complete the job and export the collection to Salient. Unfortunately, the export included a large number of encrypted files that could not be decrypted outside of the client’s Microsoft 365 environment. This was a direct result of sensitivity labels on company confidential information that had not been decrypted prior to export.
Had the operator been well-versed in the different decryption options available in the Purview eDiscovery tools, the encrypted data would have been immediately available for early case assessment in Microsoft 365 and if potentially relevant, exported in its original decrypted format.
The challenges and pitfalls of eDiscovery in Microsoft 365
What does Microsoft Purview offer a legal team? How can the technology be used for eDiscovery activities and what sorts of challenges might you face?
Microsoft Purview eDiscovery is a powerful tool in the right hands. Our experts share the causes and effects of over- and under-collection that are symptomatic of reactive eDiscovery requests.
Encrypted data can create blind spots that, without expert knowledge, could go unnoticed during the search/collection/export of data during an eDiscovery case.
Email inboxes are a treasure trove of information. However, long term retention in email archives and preserving the relationships between emails, links, attachments can pose eDiscovery challenges.
Indexing is the process of producing a searchable catalogue of files, messages and other content in a set of electronic data. Understanding how indexing works in Microsoft 365 is vital for acccurate and complete eDiscovery.
Microsoft Purview’s eDiscovery tools can be directly affected by broader data governance and compliance issues. Our experts explore issues like data sovereignty and data residency in eDiscovery.









